
Intro
securing your blog is not an easy task and however at the same time it doesn’t have to be a complicated task and should be one that you take very seriously. If you’re doing any level of business or you plan to grow your blog and you haven’t considered security yet, then now is the time to sit down and make things happen.
The last thing you want to do is put tons of time and effort into a system only to lose it all because you didn’t take some simple precautions that can take under less than an hour to implement. Below is a list of some of the top security tips you can implement on your blog.
Overview
- Don’t Invite Attacks
- Backup Your Entire Site
- User Credentials
- Limit File System Access
- Use Quality Code
- Use Secure Channels
- Harden Your Admin
- Hacker Troubleshooting
- WordPress Security with plugins
Don’t Invite Attacks
This is probably the biggest overlooked security advice anyone can offer and many times can go much further than any technical implementation suggested. The main idea here is to not invite attacks to your site. That simply means being respectful, showing respect, and just plain out being a nice man or woman. Keep your online reputation to its highest and avoid offensive communication that could invite any type of attack. Sometimes these attacks can come in the form of a denial of service attack. This is where an attacker floods your server and nobody else can surf your site, which has happened to many politicians and individuals who offended somebody through deed or action.
It is also important to watch any claims you make or sponsor. Don’t make claims that your site is super secure or that you have yet to be penetrated. This is just asking for an attack or in some cases a challenge. Leaving rude or unthought-out responses in any type of electrical format that can be used against you later on is, something you should avoid at all costs. The old proverb, “do unto others as you would have them do unto you,” should ring loud in your life on the grid and should always be in the back of your mind.
Backup Backup Backup…
Be sure that you not only back up all your files, but your entire database on a frequent basis. Make sure this backup resides somewhere else than where your actual site is located. A backup can also serve well if your site does get hacked and you need to restore it to a pre-hacked state. There are lots of plug-ins on the market that can do this, but be sure the plug-in supports both your database and your file system. If you’re interested in a free plug-in, we have one that will work for you. It’s written by the great folks right here at LifeInTheGrid.com and is called the Duplicator.
User Credentials
The username, ‘admin’ should be removed completely. This is the common administrator username for WordPress and is an easy guess for most hackers. All passwords should have the following characteristics:
- at least eight characters in length
- contain a special character, such as (%, @, !)
- contain a number
- contain an upper and lower case letter
Limit File System Access
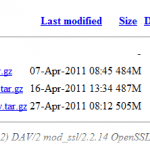
Don’t allow your Web server to serve up anything but individual files such as images, css, js and php files. By default on most web servers, if the file index.html or index.php is not inside a directory, then the web server will list the directory and other files inside that path. To avoid this, simply add the following line of code to your (/your-worpress-root/.htaccess) file that resides in the root of your WordPress site.
- Options All -Indexes
Furthermore you should lock down your wp-content directory to only serve up the necessary web files. Place the following snippet below in your (/your-worpress-root/wp-content/.htaccess) file. Again, if its not there then just create the .htaccess file.
AuthUserFile /dev/null AuthGroupFile /dev/null AuthName “Access Control” AuthType Basic order deny,allow deny from allthe # whitelist work IP address allow from 56.0.0.1 #My House allow from 56.0.0.2 #My Hostspot allow from 56.0.0.3 #My Work
Use Quality Code
When working with any code that is not part of the core WordPress system, always use extra caution as to whether you will use it or not. Read all the reviews and even do a Google search to see what people are saying about the plug-in or theme. It is highly recommended that you have a localhost version of your WordPress installed, this way you can test the plug-in locally in a development environment before pushing it to a production environment.
Every plug-in and theme that you install creates additional access points for hackers to attempt to get into your system. If you’re not using a theme or plug-in then don’t have it on your production system (don’t even leave it deactivated). When a new WordPress update comes out it’s recommended to update sooner than later. While most updates from WordPress are pretty solid, it’s still a good idea to test the new update locally then push to your production site.
Use Secure Channels
Anytime you send security credentials or login to a system, your credentials are not encrypted. This is unless your using an encrypted protocol and any potential hacker has the ability to easily see your login and password. So when you transfer files (FTP) or login to your WordPress administrator you should do it over a secure channel such as SSL or SSH. Below are a few good tips to use when you use your credentials to sign into any part of your WordPress site.
Logging into the administrator
The following setting can be used in your wp-config.php file, but only works if the server your WordPress site resides on supports SSL.
- define(`FORCE_SSL_LOGIN´, true);
When Using FTP
If you’re using an FTP program such as FileZilla and your hosting provider supports SFTP (secure FTP) then be sure to enable it. Don’t get lazy and plan to do it sometime, just do it now and set your mind at peace. The process is super simple, by configuring your settings to always use it you can be secure with every transfer from here on out. See the picture below for an example of where to set this in FileZilla.
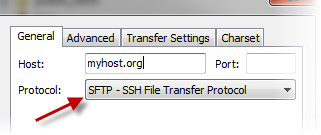
If you’re using a default remote directory to drill down into your theme folder or WordPress site, then you might have to change this for SFTP since some hosting providers have this mapped a little bit differently.
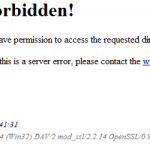
Harden Your Admin
Your wp-admin directory is very important in that it actually contains a deeper penetration into your database and file system. Therefore, it’s important that none of the files in this directory can be accessed apart from required users. This can easily be done by editing the .htaccess file located in your wp-admin directory (If it doesn’t exist just create one). Add the following to the file where every ‘allow from’ is a location that you will be browsing to from your WordPress administrator. If you need to browse outside of these IP ranges, just SFTP into your hosting account from wherever you are and add your current IP to the list. Here is what your current IP is.
AuthUserFile /dev/null
AuthGroupFile /dev/null
AuthName “Access Control”
AuthType Basic
order deny,allow
deny from allthe
# whitelist work IP address
allow from 56.0.0.1 #My House
allow from 56.0.0.2 #My Hostspot
allow from 56.0.0.3 #My Work
Hacker Troubleshooting
If your site does get hacked and you follow the advice in the backup section above, then you should be able to restore your site to a pre-hacked state. There are a couple ways to see where and how you got hacked and most of those signs will appear in your database or in your file system. We’ll run through two ways to check both.
FileSystem
Assuming you have a snapshot of your file system before it was hacked, you can find out which files changed or which files were added by doing a comparison of the snapshot in your currently hacked system. Just download a copy of UltraCompare (use free trial if you need) and compare the snapshot versions. If you want to just compare the differences of a single file, you can use a tool such as DiffMerge or UltraEdit.
Database
To see where a database entry may have gotten hacked you can easily export your database into a file, then grab a copy of your pre-hacked database exported file (good backup plug-ins will support generating this file, see Duplicator) and compare the following files with either of these tools (DiffMerge or UltraEdit).
WordPress Security with Plugins
Almost all of the items above are general in nature and you don’t necessarily need to be running a WordPress site. Since this post was originally created I noticed that there was not anything that really talked about WordPress security from a plugin standpoint. A commenter “Riaan Aggenbag” left some good tips for WordPress plugins that help harden your site, the plugins he mentioned were:
– Better WordPress Security
– WordFence
Since then I have used them both and they are great plugins! While WordFence I wouldn’t necessarily label as a must have, I did really like Better WordPress Security and would highly recommend that you install it on every WordPress site you have.
Belows is a handy infographic provided by OnBlastBlog.com
Credit: On Blast Blog

Additional Resources
– Hardening WordPress wordpress.org
– Changing File Permissions wordpress.org
– Apache Security apache.org
– Linux File Permissions tuxfiles.org
– WordPress Security wpbeginner.com
13 thoughts on “Top Security Tips for Your WordPress Site”
Comments are closed.
Just used Duplicator for the first time and couldn’t believe how easy it was – literally a few clicks with no techie stuff included and BAM, done!
After a client WP site was hacked I tested many free plugins and found the following the best (maybe someone out there needs it)
– http://wordpress.org/extend/plugins/better-wp-security/
– http://wordpress.org/extend/plugins/wordfence/
All the best And thanks for the awesome insights you share!
Riaan
Hey Riaan,
Thanks for getting in touch! I use both of those plugins on several WP sites, very good recommendations!
Better WP Security does lots of things. Iff you know what you are doing, they are probably useful (if rather paranoid).
But if you do not, one of the things it will do is mess up your site to the point where you need to start changing the site’s database by hand to repair things.
I now prevent clients from installing it.
They get Limit Login Attempts installed for them, along with advice not to let anyone they do not completely trust have an account. The plugin stops password attacks, and the advice covers WP’s annual user privilege exploit. The server has a firewall that blocks various other attacks.
That, and the advice in the article, seems to work without them risking BWPS.
Thanks for your feedback Ian! Yeah I agree BWPS can sometime cause some issues and if your not proficient with editing .htaccess files it can really cause issues…
Hi there, I just seen that occasionally this website shows a 404 server error. I thought you would be keen to know. Thanks
Hi there!
I find good security plugin and recomend it for you. Most from this functions from this post this plugin has . You can find it from this sites:
http://supsystic.com/
https://wordpress.org/plugins/security-by-supsystic/
Good information. Lucky me I recently found your website by chance (stumbleupon).
I’ve book-marked it for later!
Hi there, all the time i used to check weblog posts here in the early hours in the dawn, for the reason that i enjoy to gain knowledge of more and more.
Hi there mates, its fantastic post concerning cultureand fully defined, keep it up all the time.
Quality articles or reviews is the main to interest
the visitors to pay a quick visit the website, that’s what this web site is providing.
whoah this weblog is magnificent i like studying
your posts. Stay up the good work! You recognize, many people are hunting around for this info, you could
aid them greatly.
Very good article. I certainly love this site. Keep it up!
Thanks for every other informative website. The place else could I get that
type of information written in such an ideal means?
I have a undertaking that I’m simply now working on,
and I’ve been at the glance out for such information.